Have you ever wondered why computers suggest flash drives to be properly ejected? Have you been hesitant to ask friends how they can afford so many cables that aren’t always affordable?
Like the normal computer or internet user, you probably have lots of questions you’re anxious to ask someone else. Don’t worry, we are here to help. We’ve gathered 10 of the most common tech questions in a list below, each with their explanations and simple remedies.
1. Should I be worried about my online privacy? If yes, how can I make sure I’m protected?

You’ve probably heard someone say, “If it’s on the internet, it’s not private.” That’s not totally true, however, since there are several ways you can ensure your privacy across digital platforms and services. Still, you should be concerned. Not everybody may be interested in your things, but somebody probably is.
Not a lot of users know or care about their digital footprints. Or if they do, they don’t usually know particular circumstances wherein personal data could be at risk. If you want to be more careful from now on, follow these tips:
- Don’t put out all of your personal/business info. Identity theft remains one of the most serious issues in this internet era. Sharing every little thing about yourself on different platforms can make you vulnerable to cybercrime.
- Don’t use the same password for all of the websites you use. Having the same one will allow hackers to juice out all your info with ease.
- Use a VPN to stay safe. When it comes to your money, utilize app security, keep the important numbers/info to yourself, and don’t carelessly click on hyperlinks from untrusted emails.
2. What does malware do?
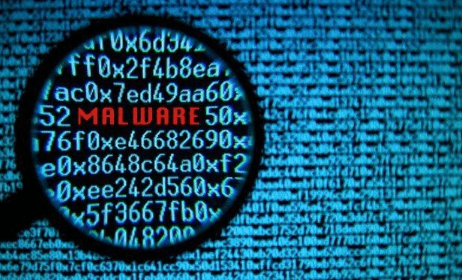
Malware is the umbrella term used to identify viruses, Trojans, spyware, adware, and other malicious programs that are widespread across the web. If you’ve encountered viruses before, then you’re already familiar with their effects. Other types of malware, however, can cause various impacts or damage.
You’re well served to really familiarize yourself with what each type does to your computer, but we’ll summarize them to get you started:
Trojans
Appear as normal apps but usually run underground codes that can allow someone else to monitor you or take over your PC.
Viruses
Work like real-life ones, disabling functions or tasks and spreading the fastest through USB or thumb drives.
Adware
Is short for “advertising-supported software” which automatically plasters unsolicited ads in browsers and websites. Most adware is sponsored or designed by advertisers to generate revenue.
Ransomware
Is the type that basically holds the computer captive until the demanded ransom is given. All administrative access is restricted. This is often regarded as one of the more serious forms since it demands real payment. It can be acquired just like normal viruses, either via downloaded files, network vulnerabilities, or installed programs.
Spyware
Functions by stealth, mainly spying on user activity. Spying can include data harvesting, keystroke collecting, and software or settings modification. Like ransomware, it’s serious and should not be underestimated.
Rootkit
Gains remote access or control over a computer without being detected.
Worms
Are the most common malware type. They typically exploit OS vulnerabilities and cause damage by overloading servers and consuming bandwidth.
The most certain way you can protect your computer against malware is to arm it with an antimalware program. You can choose free versions or afford added security by purchasing premium. Be careful with your internet use as well – don’t visit untrusted or unsecure sites, don’t download from sketchy sources, and don’t click on just about anything without a thought or two.
3. What happens when a website I frequent gets hacked?

There are telltale signs you can look out for when a website is hacked. Popups may appear, sudden tabs may open, browser addons you don’t know are already there, or your homepage may have changed.
Hackers are often on the hunt for usernames and passwords, so if you have strong protection against that, you don’t have to worry as much. You can enlist the help of a good password manager or you can make sure all of your passwords are different and are hard to crack.
4. Should I really “eject” USB/flash/thumb drives?
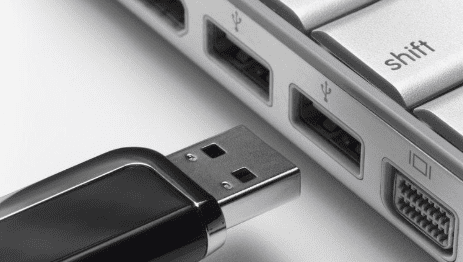
Yes, you should. When your computer prompts you to “safely remove” the external device, it wants you to prevent data loss by enabling it to finish everything in queue. While sudden removal won’t incur definite loss in Windows, experts recommend safely ejecting in all operating systems.
The process in which the computers warn you is called “write caching”, which in turn is intended to improve performance. When you do something as simple as copying a file, the display will tell you that the task is complete. But, technically speaking, the device is waiting for other instructions so it can perform them efficiently all at once.
5. Why are cables so expensive?
The truth is, not all of them are. You don’t always need to spend a ridiculous amount just for one HDMI or charger cable. Why companies price accessories so high is because they know you’re going to buy them anyway.
In the old days, cables were understandably expensive. Today, however, they can be produced more easily, so they shouldn’t always be stretching your budget. If you want to save money on your gadgets, check out refurbished products.
6. Should I use public Wi-Fi?

Unless the need is dire, experts advise very rare use of public networks. Even though a network has its password, people on the network can still see and monitor activity. If you happened to use one with cybercriminals on it, chances are they could steal your information.
When you have no choice but to use a public network, make sure you do the following: route your traffic through a VPN, use HTTPS, disable “sharing” before confirming connection, and sticking to secure sites only.
7. What should I do to preserve my phone’s/laptop’s battery health?
It’s important to note that, in the case of today’s batteries, nothing you can do will prevent their inevitable deaths. Still, you can utilize tactics to help prolong your gadget’s battery life.
Ignore the pervasive rumor that it is beneficially to “fully discharge your phone.” Lithium ion batteries, which power most of our phones and laptops, ideally last longer on slow and shallow discharges. To avoid causing fast damage, try to keep them cool and don’t leave them plugged in after they’re fully charged. You can also try to learn when a battery starts dying so you can replace it before it causes other damage to your phone or laptop.
8. How can I find out if an email is spam?

The subtler spam emails usually come from phishing attempts. Phishing mainly involves spammers trying to make their emails look like they come from legit sources. When someone is tricked into clicking the given hyperlink, the message will spread to contacts in the mailing list. Some hyperlinks will also lead to disguised sites, which can trick anyone into providing personal, crucial info.
Luckily for you, powerful anti-phishing software can help you figure out which messages are malicious. You can also try to learn how your network operates – when a unit starts communicating with another that it doesn’t usually interact with, then that’s when you’ll know there’s something wrong.
9. Why is my router prompting me to reset it over and over?
You’ve probably tried resetting your router when your internet was acting up. After every reset, you find it seamlessly working again, until the issue resurfaces. The question is, why does it happen?
There are many things that may be causing it, such as overheating, too much traffic (number of people using it), or that it needs to be replaced with a new one. You can try to fix your router on your own – a quick Google search can run you through some methods – or you can always contact your service provider to have it replaced.
10. Will I get caught if I download content from BitTorrent or other Torrent servers?
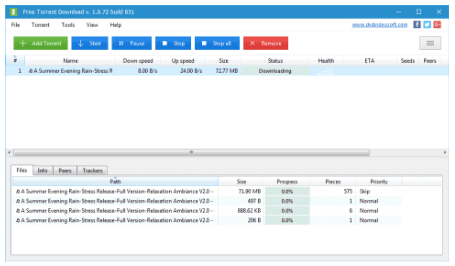
Although it seems pretty lax, yes, you can still get caught. Some media companies are still prowling for users illegally downloading their content. Internet providers can even monitor your activity to see if you’re torrenting anything.
As implied, the legalities are not so heavy on the users today, primarily because it’s difficult to file complaints against hundreds and thousands of users scattered across the world. You can keep yourself anonymous by using certain tools. Remember though, that nothing is foolproof.
Hopefully, we have answered some of your most common tech questions. Let us know if you’ve got other questions in mind!