Android is considered to be one of the most secure mobile platforms on the planet. Sure, a few viruses slip through the gates and infect several users but, most of the time, Google’s efforts are effective in protecting users from online threats. Unfortunately, online security firm Skycure has discovered a loophole that can put Android users at risk. This loophole targets those who use Android for Work, which means that personal security isn’t the only issue here since sensitive corporate information is also at risk.
What is Android for Work?
Android for Work was introduced in 2014 along with Google Play for Work. These two services fulfill businesses’ needs by allowing enterprise-level apps to coexist with personal apps without interacting with each other. This proved to be a big hit among business owners and employees since they no longer had to bring a work phone along with their personal phone. With just one device, they could access work-related applications while keeping their personal stuff separate.
Technically, the service is no longer called “Android for Work” since Google renamed it to simply “Android” late last year. However, nothing much has changed. The major difference is that many of the features found in the enterprise service are now a core part of the Android and Google Play for the general public, so there’s no need for separate branding.
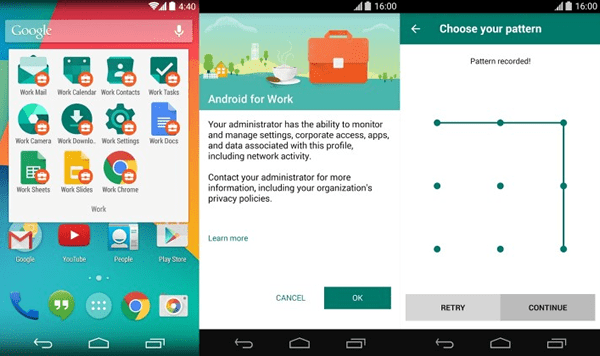
One of Android for Work’s biggest benefits is that it safeguards work-related data. IT administrators can use special tools to protect work profiles so, even when enterprise and personal apps are used side-by-side, there’s minimal risk of security breaches — at least in theory.
How Android for Work Can Be Breached
Skycure proved that Google’s defenses are far from being impenetrable. During the 2017 RSA Conference (which took place on February 13 to 17), the company discussed how an innocent-looking-but-actually-malicious app can “bridge” the separation between personal and enterprise applications. When this happens, the harmful app can obtain users’ information — including sensitive corporate details.
Phone Notifications
As Skycure demonstrated during the RSA Conference (and discussed on their blog), malicious apps can breach Android for Work’s defenses by using phone notifications. In devices with Android for Work, users can receive enterprise-related notifications alongside any notifications from their personal apps. If a malicious app is given the permission to access notifications (and this is something that almost every mobile application nowadays can do), it can collect enterprise information and pass it on to cyber criminals.
Skycure demonstrated this using a personal app that allows users to mirror notifications from their Android device to their PC, presumably so they won’t have to glance down at their phone every now and then. For the app to work, users need to give it the permission to view and take action on their notifications. The problem lies in the fact that Notification Access is given as a device-level, not app-level, permission so the malicious app can access both personal and enterprise-related notifications.
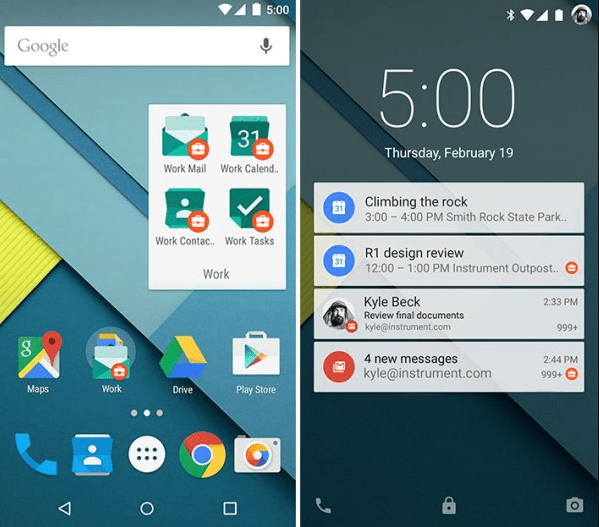
The app definitely works as advertised, but what users don’t know is that it’s also copying their notifications and sending them to hackers — who can now read their work emails, office calendar reminders, and chats with their managers and coworkers.
Even worse: a hacker can further take advantage of this situation by using the “forgot password” feature in apps and websites. Usually, when a user clicks the “forget password” link, the service provider sends him an email to allow him to reset his password. If the hacker already has access to the user’s email account (through the malicious notification-mirroring app), he can intercept the email and use it to give himself access to the user’s other accounts. The user won’t even know that this happened since the hacker can dismiss the notification right away and archive the email.
Accessibility Permissions
Android’s Accessibility Service is helpful for users with visual impairment since it translates on-screen text into an audible narration. To make this possible, the service needs to have access to all the controls in the device (both for reading and writing) — something that can be hijacked by attackers.

To illustrate this, Skycure used a personal app called StickiWiki that allows users quickly look up information on Wikipedia by simply typing “@wiki” in any application. To perform this function, StickiWiki has to ask permission to access all content on the screen so it would know when to perform a search on Wikipedia. There’s nothing wrong with this — unless StickiWiki is a malicious app. If it is, it can use its Accessibility Permission to access both personal and enterprise apps and render Android for Work virtually useless.
Possible Solutions

One of the best ways to work around these vulnerabilities is to require employees to use a separate smartphone for work-related tasks. If this is not possible, it’s advisable to use third-party apps that offer mobile security on top of Android’s built-in defenses. Of course, users must do their part and ensure they’re not downloading unsafe apps.


