According to the US Cybersecurity and Infrastructure Security Agency (CISA), “most users get viruses from opening and running unknown email attachments.” The agency goes on to say that opening a malicious email attachment allows hackers to alter your files, steal your credit card information, or worse. Here’s everything you need to know about which email attachments are safe to open and how to scan an attachment on a Windows 10 computer.
Never Open Email Attachments Marked as Spam
By default, most email clients (like Gmail, Outlook, and Yahoo Mail) scan your email attachments for viruses. Most suspicious emails are either automatically deleted or filtered out from your inbox into a folder marked “Spam.”
While it is safe to open any emails, you shouldn’t click any links or open any attachments in emails marked as spam.

Unless you are using very old software, you won’t get a virus just by opening an email anymore. This is because most viruses require you to take some sort of action (like opening an attachment or clicking on a link) in order to infect your computer these days.
Only Open Email Attachments from Trusted Sources
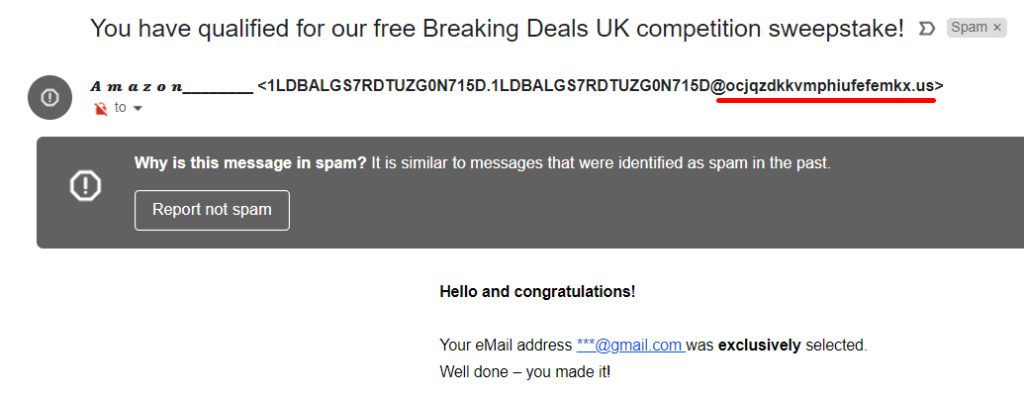
To protect yourself from malicious email attachments, the Federal Bureau of Investigation (FBI) warns you to “never open an email attachment from someone you don’t know.” The agency also advises you to “carefully examine the email address” before opening an attachment.
Hackers have the ability to “spoof” (or fake) an email address to make it look like it’s from your boss, a family member, or even a major company like Apple or Microsoft. So, before you open an email attachment, you should always check the sender’s full email address before opening an attachment.
For example, if you get an email from Amazon, the returns email address should end with @amazon.com. If the email address doesn’t match the sender’s name, or it looks suspicious at all, you should not open the attachment.
The Department of Homeland Security (DHS) says you can also identify malicious emails by looking for spelling and grammar mistakes, as well as messages that address you by the wrong name or emails that don’t contain any content other than an attachment.
Hackers even have the ability to take over an email account and send malicious attachments with their email address. So, the FBI recommends you contact the sender to confirm they sent you an attachment before you click on it. If the email is from your bank or credit card company, you should go to their official website and find a way to contact them from there.
Only Open Email Attachments with Safe File Extensions
Once you know an email is from a trusted sender, hover your mouse over the attachment to see the file extension. This is the last three or four letters that appear after the period in a file name that lets your computer know which application can open the file.

Images, Video, and Audio Files:
Email attachments that contain images, videos, and audio files are generally considered to be the safest to open. These include files with common extensions such as JPG, PNG, GIF, MOV, MP4, MPEG, MP3, and WAV.
However, it is important to note that, even if an image looks safe, it could be another type of file in disguise. So, you should only open an attachment if you know who it is from, and you were already expecting the attachment.
Office Documents:
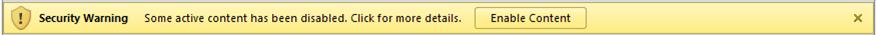
Microsoft Office documents can contain “macro” viruses, which are hard to detect because they are written in the same language as programs like Word, Excel, and PowerPoint. These include files with extensions like DOC, DOCX, XLS, and PPT.
The macro will not be activated automatically unless it is from a trusted location. So, in order to be able to edit the document, you will have to activate the macro manually by clicking the Enable Content button at the top of your screen. However, Microsoft warns you not to do so “unless you’re certain that you know exactly what that active content does.”
Executable Files:
One of the most dangerous types of files that hackers attach to emails is an executable file. If you open this type of file on your computer, it will almost certainly contain malicious software (also known as malware).
If you are on a Mac computer, you also want to watch out for DMG files, which can also be used to install malware on your computer.
Compressed Files:
Certain compressed files are also not safe to open. The most common of these have ZIP or RAR extensions. A compressed file usually contains multiple files that have been made smaller, and you won’t be able to know what they contain until you open them.
If you open a compressed file, and it has an EXE file inside, you should only run it if you absolutely know what it is and who it came from.
Never Open Email Attachments with Double Extensions
Sometimes, email attachments will look safe at first glance, but if you look closer, you will notice the file name has two extensions. For example, a file name might look like an image, but it has a name like “file.jpg.exe”. This means it’s not a JPG file, but an EXE file because the last extension at the end of the file name is all that matters.
Any file with a double extension is most likely a virus, and you should never open it to be safe. If you want to make sure, you can scan it first. Here’s how:
How to Scan an Email Attachment on Windows 10
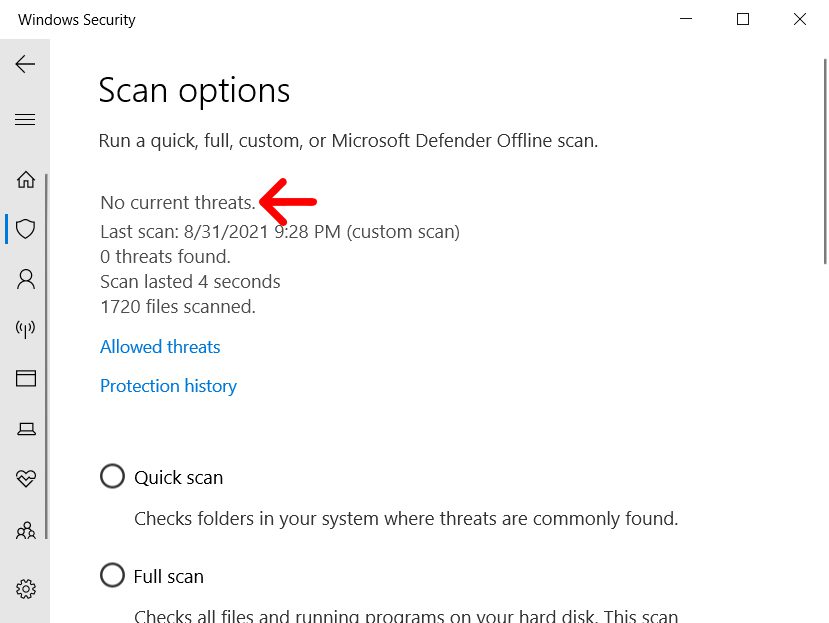
To scan an email attachment on a Windows 10 computer, download the file, but don’t open it. Then right-click the file and select Scan with Microsoft Defender. When the scan is complete, you will see the results at the top of the Settings window.
What to Do If You Opened a Dangerous Attachment
If you accidentally opened an attachment with a dangerous file extension, you should change your email password right away. You should also contact your bank or credit card company and let them know what happened, so they will be on the lookout for suspicious charges to your accounts.
Immediately after opening a dangerous attachment, you should run your computer’s anti-virus software. Otherwise, you should download and install anti-virus software on your computer. To find out more, check out our list of the best anti-virus programs for Windows PC. If you think your computer is still infected with a virus, check out our guide on how to remove malware from a Windows 10 computer.


